Risk Acceptance Form Nist
Risk Acceptance Form Nist - Approaches, methodologies, implementation guides, mappings to. Web this form is to be used to acknowledged, justify, and/or document risk acceptance of a known deficiency. Web this is a listing of publicly available framework resources. Web nist risk management framework overview • about the nist risk management framework (rmf) • supporting publications • the rmf steps. Raf field descriptions name, title, and department of originator:. Web this document provides guidance for carrying out each of the three steps in the risk assessment process (i.e., prepare for the assessment, conduct the assessment,. Web the federal risk and authorization management program or fedramp has been established to provide a standard approach to assessing and authorizing (a&a). Da form 7632, jul 2023 created date: The system/project manager is responsible for writing the justification and the. Web risk acceptance form responsible individual’s information summary of request (risk to be accepted).
Web managing organizational risk is paramount to effective information security and privacy programs; Approaches, methodologies, implementation guides, mappings to. Web risk acceptance form responsible individual’s information summary of request (risk to be accepted). The level of residual risk that has been determined to be a reasonablelevel of potential loss/disruption for a specific it system. Web security risk acceptance form (raf) for assistance in completing this form please see the following link: The system/project manager is responsible for writing the justification and the. Web instructions for risk acceptance form this form is to be used to justify and validate a formal risk acceptance of a known deficiency. Web the federal risk and authorization management program or fedramp has been established to provide a standard approach to assessing and authorizing (a&a). Web nist risk management framework overview • about the nist risk management framework (rmf) • supporting publications • the rmf steps. Benefits of accepting this risk:.
Web the federal risk and authorization management program or fedramp has been established to provide a standard approach to assessing and authorizing (a&a). Web this is a listing of publicly available framework resources. Web this form is to be used to acknowledged, justify, and/or document risk acceptance of a known deficiency. Web display the appropriate national institute of standards and technology (nist) control associated to the deficiency description of the deficiency: Benefits of accepting this risk:. Cms information security policy/standard risk acceptance template of the rmh chapter 14 risk assessment. Web risk acceptance form responsible individual’s information summary of request (risk to be accepted). Web risk acceptance form this form is used to justify a risk acceptance of a known deficiency. Approaches, methodologies, implementation guides, mappings to. Web this document provides guidance for carrying out each of the three steps in the risk assessment process (i.e., prepare for the assessment, conduct the assessment,.
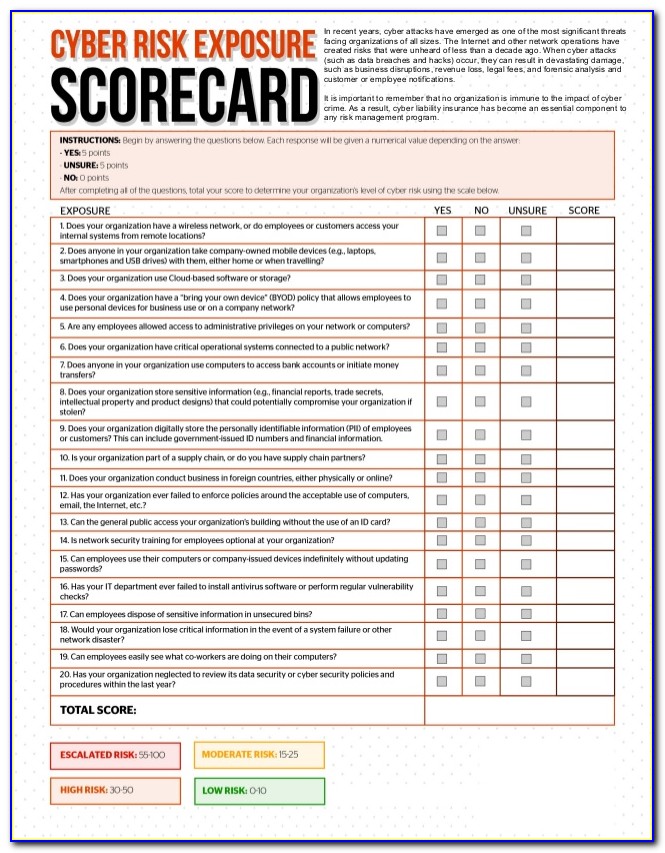
Cyber Security Risk Assessment Sample
Provide a summary of the. Web risk acceptance form this form is used to justify a risk acceptance of a known deficiency. Web managing organizational risk is paramount to effective information security and privacy programs; ® ¤ 'h}ûã ‘ cl { ž`ñ{4š æ½ µ÷èžq u/ 85 ãî¹ a baþ›|cð. The responsible party that signs this document is ultimately.
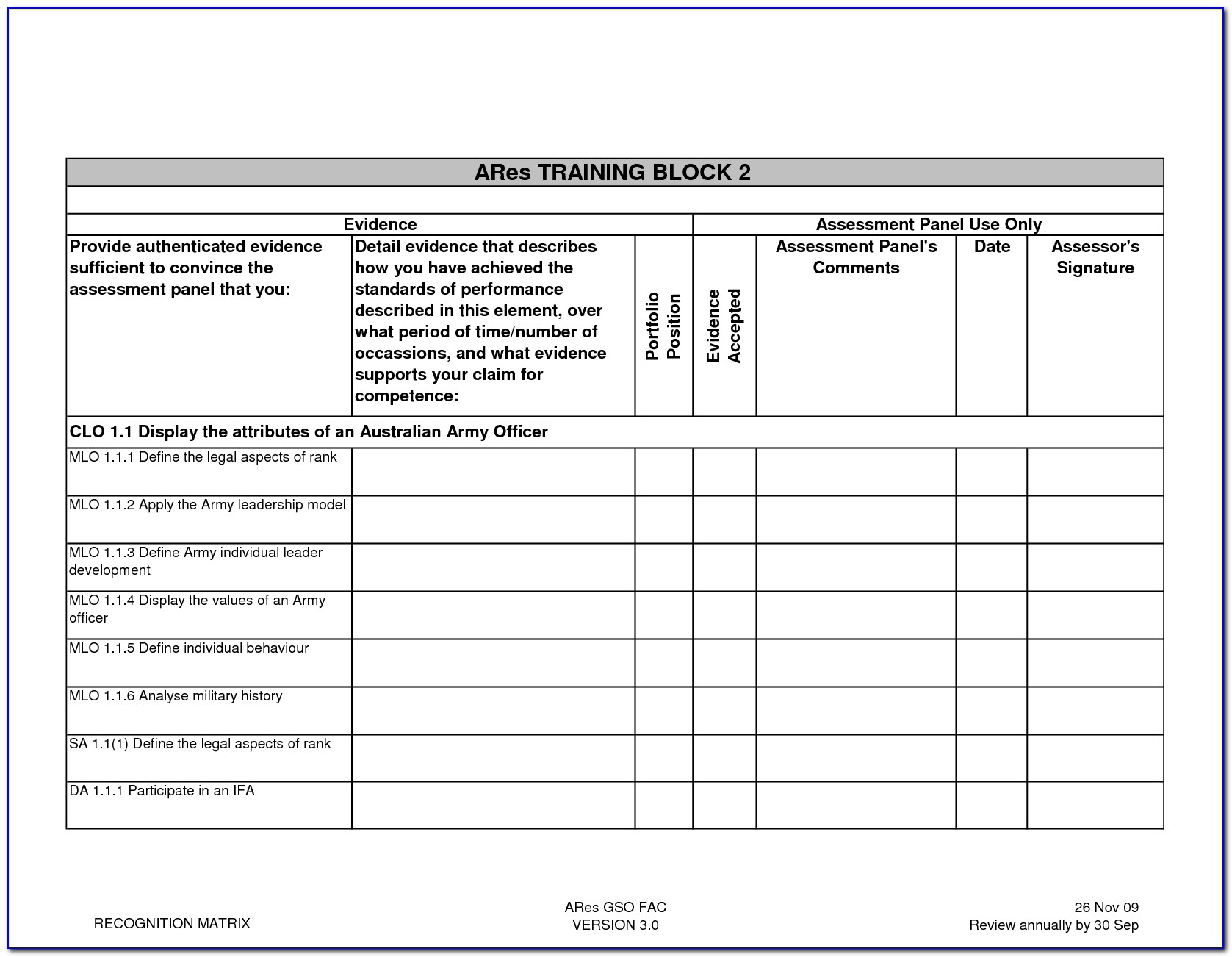
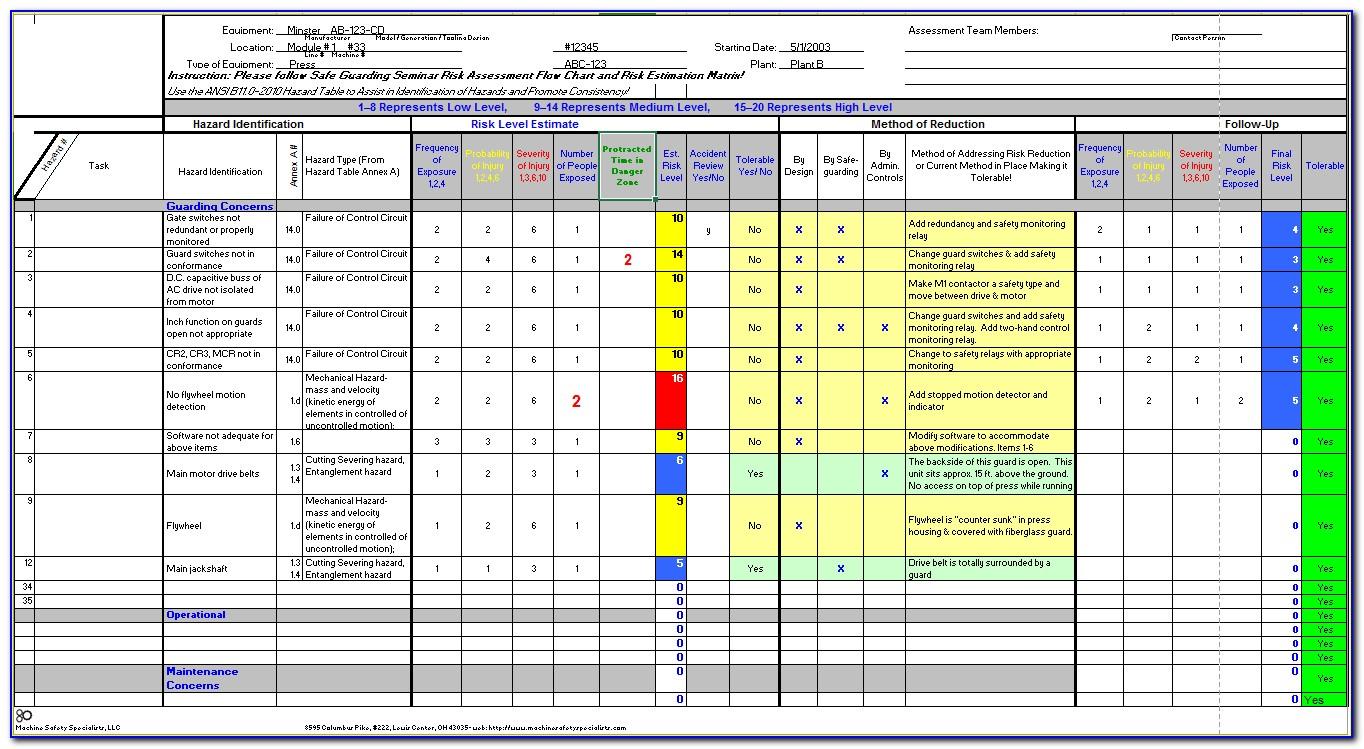
Nist Risk Assessment Template Xls
The level of residual risk that has been determined to be a reasonablelevel of potential loss/disruption for a specific it system. Web based on the risk identification and risk analysis 197 described in nistir 8286a, this nistir 8286b document describes the prioritization of 198 specific risk scenarios and. Web this document provides guidance for carrying out each of the three.
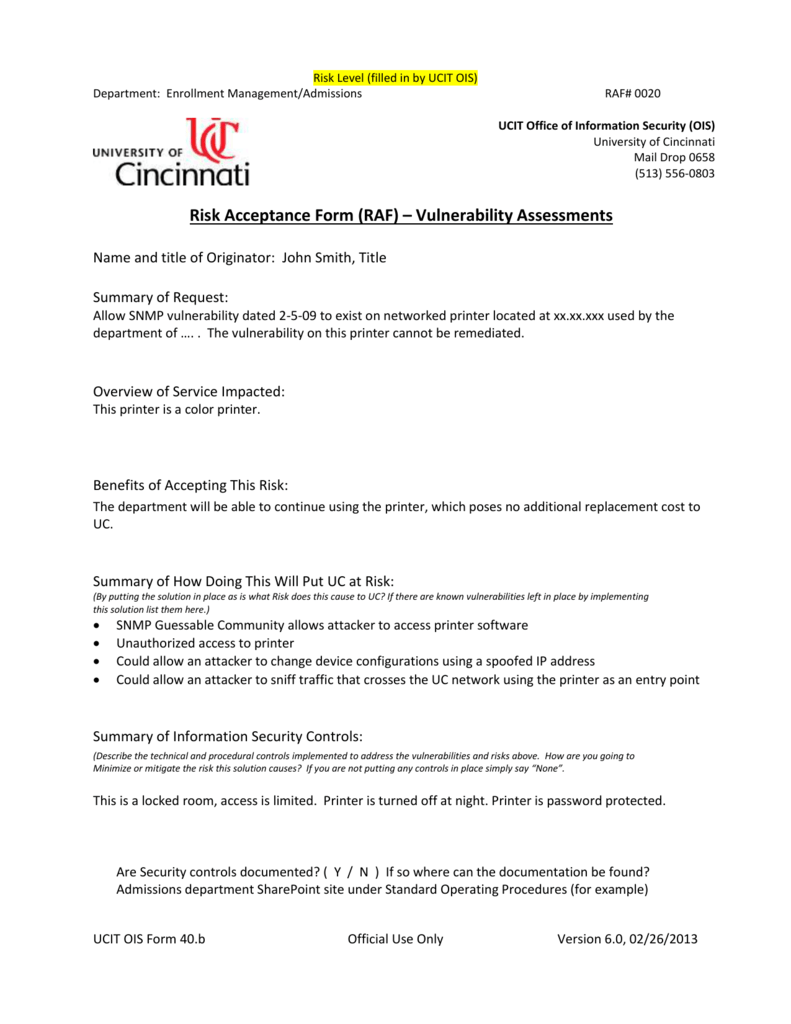
Risk Acceptance Request University of Cincinnati
Web this is a listing of publicly available framework resources. Web nist risk management framework overview • about the nist risk management framework (rmf) • supporting publications • the rmf steps. Web managing organizational risk is paramount to effective information security and privacy programs; Web the federal risk and authorization management program or fedramp has been established to provide a.
Nist Incident Response Plan Template Lovely 015 Plan Template Nist
Web security risk acceptance form (raf) for assistance in completing this form please see the following link: Web display the appropriate national institute of standards and technology (nist) control associated to the deficiency description of the deficiency: Web this form is to be used to acknowledged, justify, and/or document risk acceptance of a known deficiency. Web the federal risk and.
Nist Cyber Risk Assessment Template
Da form 7632, jul 2023 created date: Web instructions for risk acceptance form this form is to be used to justify and validate a formal risk acceptance of a known deficiency. Web this is a listing of publicly available framework resources. Web based on the risk identification and risk analysis 197 described in nistir 8286a, this nistir 8286b document describes.
Information Risk Acceptance Process
The rmf approach can be applied to new and legacy systems,. Web this is a listing of publicly available framework resources. The level of residual risk that has been determined to be a reasonablelevel of potential loss/disruption for a specific it system. ® ¤ 'h}ûã ‘ cl { ž`ñ{4š æ½ µ÷èžq u/ 85 ãî¹ a baþ›|cð. Web instructions for risk.
lecture 9 Risk Acceptance YouTube
Provide a summary of the. Approaches, methodologies, implementation guides, mappings to. Web security risk acceptance form (raf) for assistance in completing this form please see the following link: Web this document provides guidance for carrying out each of the three steps in the risk assessment process (i.e., prepare for the assessment, conduct the assessment,. Web nist risk management framework overview.
Risk Acceptance Form Threat Vulnerability
The rmf approach can be applied to new and legacy systems,. Web based on the risk identification and risk analysis 197 described in nistir 8286a, this nistir 8286b document describes the prioritization of 198 specific risk scenarios and. Certificate of risk acceptance author: Web this document provides guidance for carrying out each of the three steps in the risk assessment.
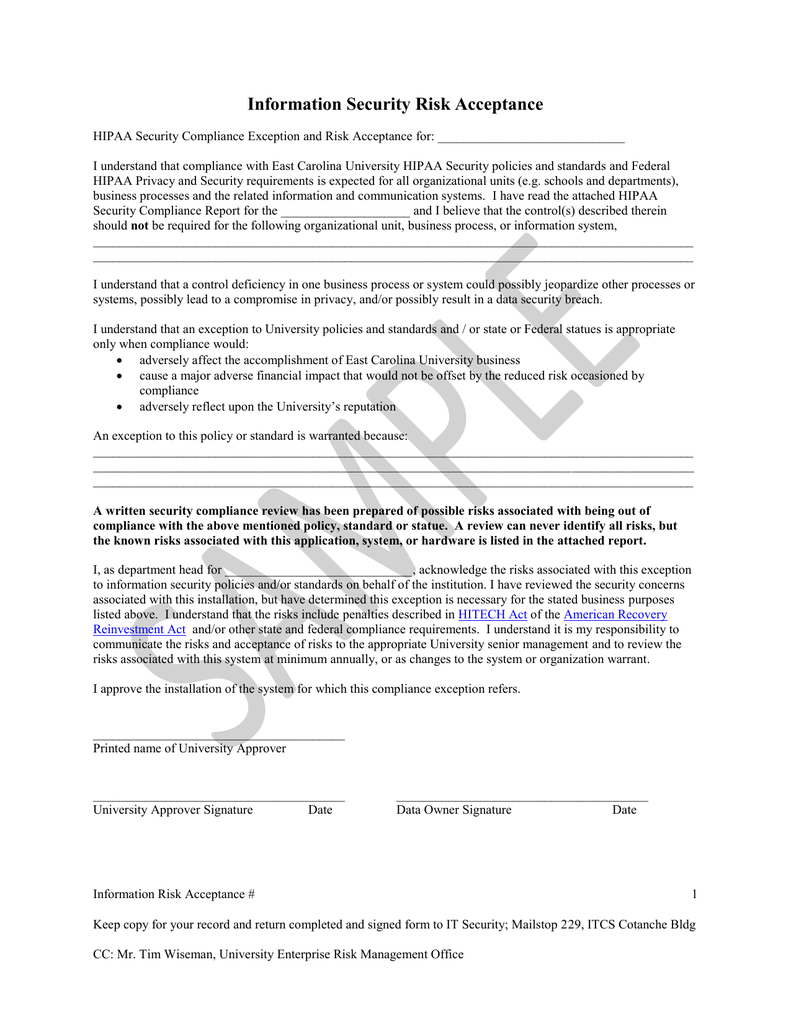
Information Security Risk Acceptance Document
Web instructions for risk acceptance form this form is to be used to justify and validate a formal risk acceptance of a known deficiency. Web this document provides guidance for carrying out each of the three steps in the risk assessment process (i.e., prepare for the assessment, conduct the assessment,. Web display the appropriate national institute of standards and technology.
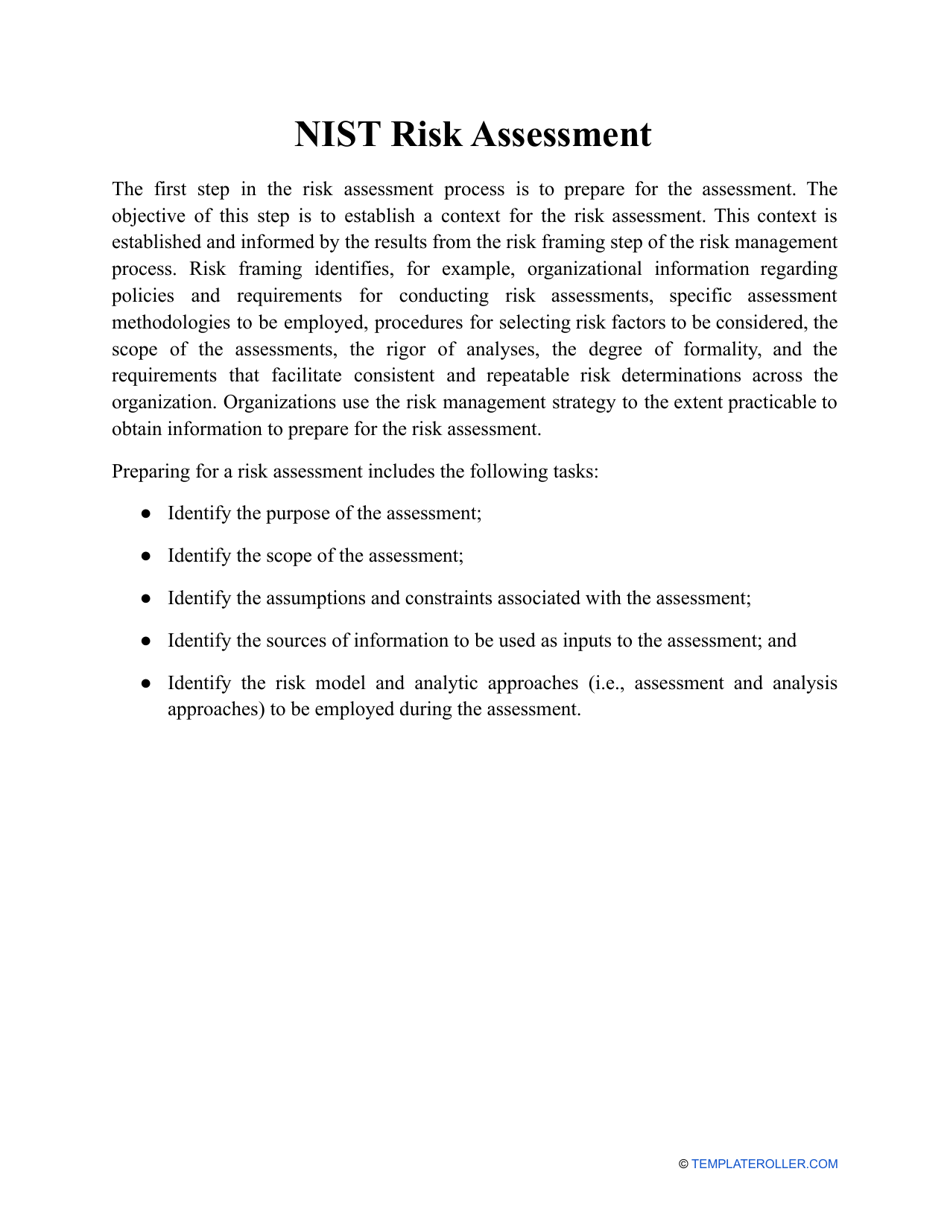
Nist Risk Assessment Template Download Printable PDF Templateroller
Web this document provides guidance for carrying out each of the three steps in the risk assessment process (i.e., prepare for the assessment, conduct the assessment,. Web the federal risk and authorization management program or fedramp has been established to provide a standard approach to assessing and authorizing (a&a). Web form & templates. Web display the appropriate national institute of.
Web This Document Provides Guidance For Carrying Out Each Of The Three Steps In The Risk Assessment Process (I.e., Prepare For The Assessment, Conduct The Assessment,.
Web form & templates. Web security risk acceptance form (raf) for assistance in completing this form please see the following link: Web instructions for risk acceptance form this form is to be used to justify and validate a formal risk acceptance of a known deficiency. Web risk acceptance form responsible individual’s information summary of request (risk to be accepted).
Web Managing Organizational Risk Is Paramount To Effective Information Security And Privacy Programs;
Certificate of risk acceptance author: Web this form is to be used to acknowledged, justify, and/or document risk acceptance of a known deficiency. ® ¤ 'h}ûã ‘ cl { ž`ñ{4š æ½ µ÷èžq u/ 85 ãî¹ a baþ›|cð. Provide a summary of the.
Resources Include, But Are Not Limited To:
Web display the appropriate national institute of standards and technology (nist) control associated to the deficiency description of the deficiency: Web this is a listing of publicly available framework resources. Web risk acceptance form this form is used to justify a risk acceptance of a known deficiency. The responsible party that signs this document is ultimately.
Web Based On The Risk Identification And Risk Analysis 197 Described In Nistir 8286A, This Nistir 8286B Document Describes The Prioritization Of 198 Specific Risk Scenarios And.
Web the federal risk and authorization management program or fedramp has been established to provide a standard approach to assessing and authorizing (a&a). Cms information security policy/standard risk acceptance template of the rmh chapter 14 risk assessment. The system/project manager is responsible for writing the justification and the. Raf field descriptions name, title, and department of originator:.